Cyber doesn’t stay in the IT department
Many business owners still hear the word cyberattack and think of it as an IT problem. That’s understandable, but it’s incomplete.
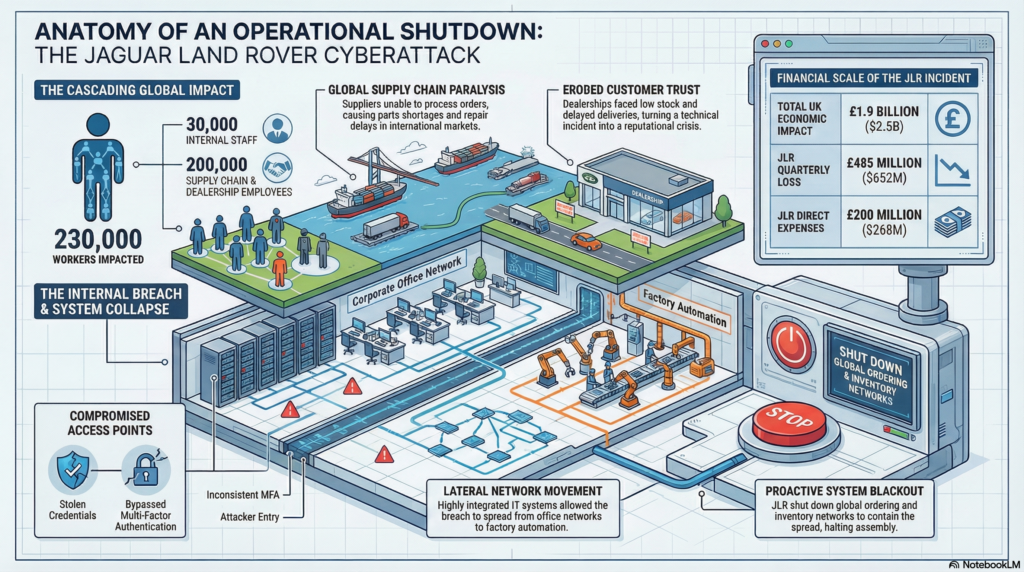
The bigger lesson from major cyber events is that the damage rarely stays inside the technology department. Once core systems are affected, the fallout can spread into operations, production, logistics, customer service, revenue, and reputation. That’s why cyber risk should be treated as a business continuity issue, not just a technical one.
What the event actually teaches
The most useful lesson from a large manufacturing cyber event isn’t the company name. It’s what the event reveals about business dependency.
When critical systems were shut down to contain the incident, assembly plants went idle, ordering and logistics were disrupted, parts availability tightened, and the impact spread outward to customers, dealers, suppliers, and related businesses. What started as a cyber issue became an operational shutdown.
Why supply chain and customer impact matter
This is where many owners underestimate the risk. They picture stolen data. They don’t picture missed deliveries, repair delays, inventory bottlenecks, or supplier relationships being strained because the business can’t function normally.
Customers don’t experience a cyber event as a technical incident. They experience it as poor service, missed commitments, inconsistent communication, and uncertainty. That can turn a systems problem into a trust problem very quickly.
Employers should also consider what happens if one of their supplies faces this type of attack. Where do you turn if you’re missing a critical part in your process that is no longer available?
What resilient businesses do differently
Prevention still matters, but resilience matters too. Leaders should ask what happens if a core system fails anyway. Can the business operate in a limited manual mode? Are there backups and workarounds for essential functions? Is there a communication plan for employees, customers, and partners?
Strong credential management, multi-factor authentication, network segmentation, vendor scrutiny, and incident response planning all matter because they reduce the odds that one problem turns into a company-wide event.
Insurance should match the real exposure
This is also why cyber insurance should be reviewed in light of operational reality. If a cyber event can interrupt production or create loss because a supplier is down, the insurance conversation should go beyond breach response costs alone.
The bottom line is simple: the real cost of a cyberattack is usually the business disruption that follows. Owners who understand that are in a much better position to plan for what actually hurts.


