Most cybersecurity training teaches employees to avoid things that get pushed at them—suspicious emails, unexpected attachments, weird links.
But some of today’s fastest-growing cyber threats work the opposite way. They are “pull” attacks: they lure people in through normal work habits like searching Google, downloading a tool, or clicking what looks like a routine verification prompt.
If your business runs on modern workflows—cloud apps, browsers, SaaS tools, connected operations—this matters. Your people aren’t being reckless. They’re being productive. Attackers are designing traps around that.
What is a “pull” cyberattack?
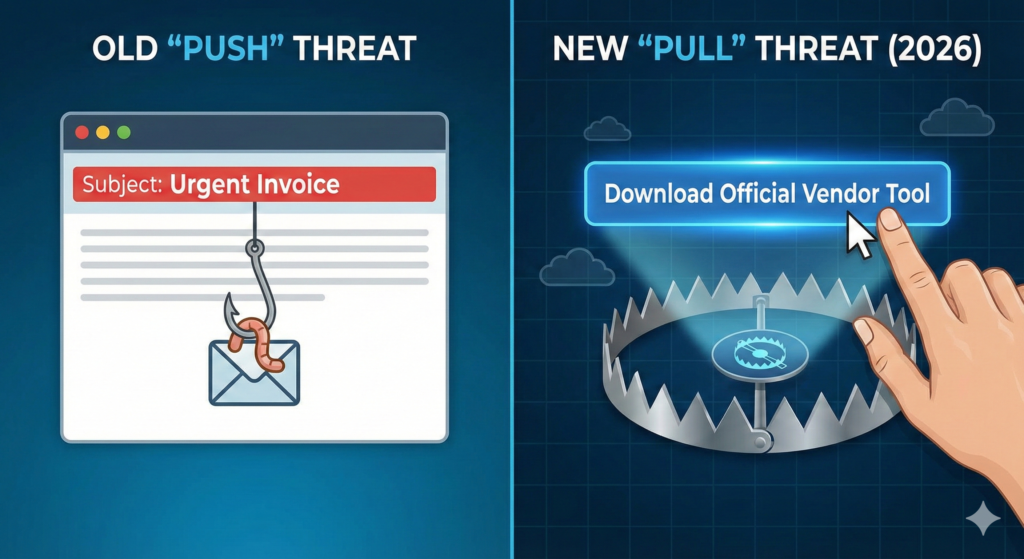
A pull attack succeeds because the user believes they are taking a normal action:
- Searching for a vendor portal
- Downloading a document template
- Updating software
- Passing a “verify you’re human” prompt
That’s why these threats can bypass training built around “don’t click suspicious emails.”
How does SEO poisoning work in real life?
SEO poisoning is when attackers manipulate search results to push malicious or compromised sites to the top—where busy employees are most likely to click.
Why it’s effective
Search results carry implied trust. Many users assume: if it’s ranked highly, it must be legit.
Common attacker techniques you should recognize
- Look-alike domains that resemble legitimate vendors
- Compromised legitimate websites used as launchpads
- Cloaking (clean content to search engines, malicious content to humans)
- Keyword stuffing to force ranking for high-value terms
Prevention-first controls that reduce SEO poisoning risk
- Use bookmarks or approved vendor portals for logins and downloads instead of searching each time.
- Turn on web filtering and endpoint protection that flags known malicious domains.
- Add training that specifically covers search-based threats—not just email phishing.
What is a ClickFix attack (and why do smart employees fall for it)?
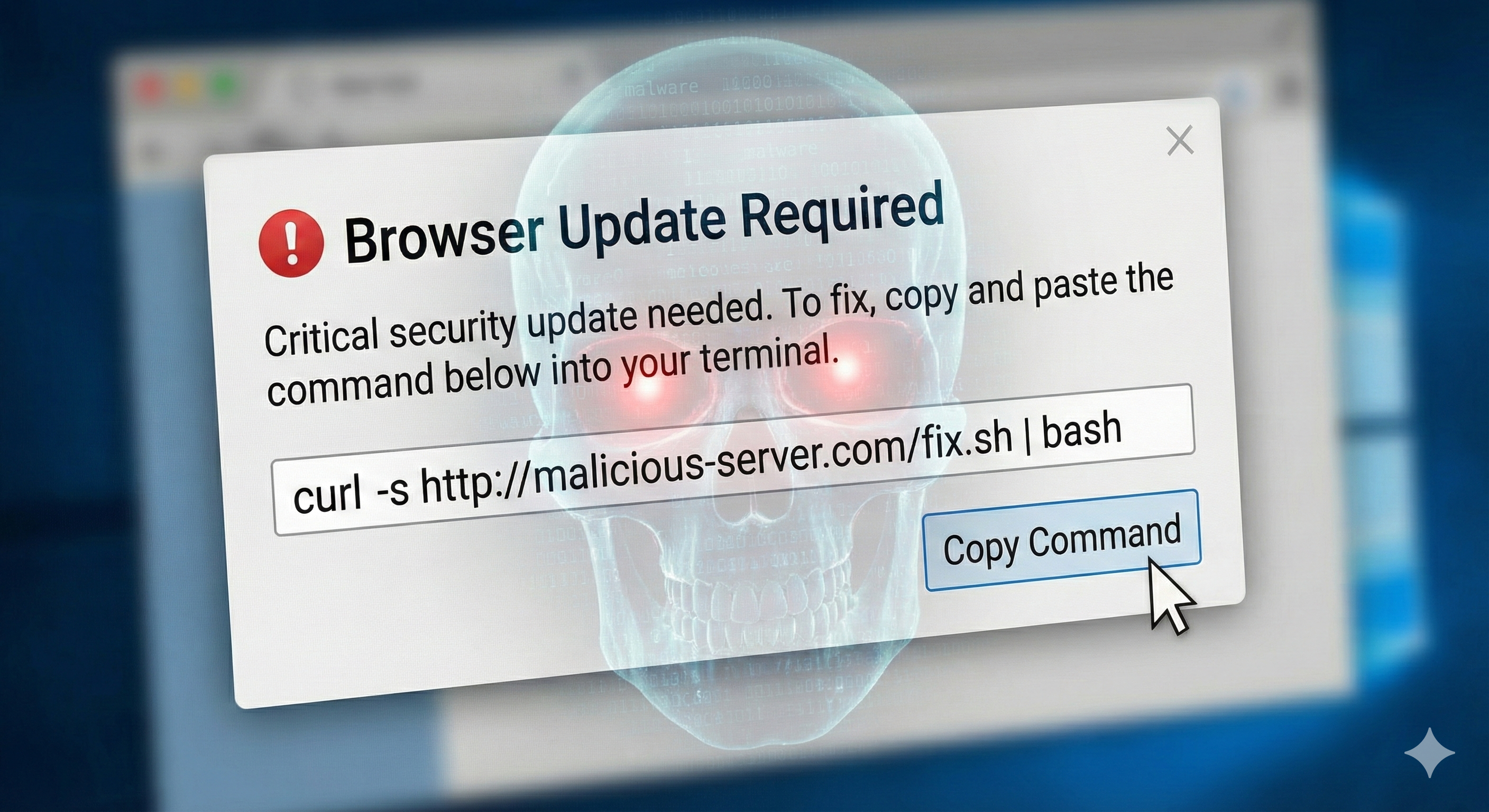
ClickFix (sometimes discussed alongside similar “fake fix” campaigns) uses browser errors or verification prompts to trick users into manually running malicious commands—often by copying and pasting instructions into a run dialog or terminal.
This is the key shift: the user becomes the installer.
Why ClickFix is dangerous
- It can sidestep traditional controls because the action looks user-initiated.
- Variations are spreading quickly across devices and platforms.
- Attackers can deploy it at scale using “crime-as-a-service” tooling.
Prevention-first moves that work
- Train employees on one hard rule: never copy/paste commands from a pop-up to “fix” a problem.
- Restrict script execution and command tools where practical.
- Keep operating systems, browsers, and apps updated with consistent patching.
Why connected warehouses and IoT operations raise the stakes
If your operations include connected systems—warehouse management systems, RFID, IoT sensors, robotics, cloud APIs—you have more attack surface. The payoff for attackers is bigger: disruption, downtime, and supply chain chaos.
Common cyber risks in connected operations
- IoT device vulnerabilities (weak authentication, outdated firmware)
- RFID data exposure (eavesdropping, manipulation, theft enablement)
- Automation manipulation (unsafe or unintended machine actions)
- Cloud and API misconfigurations (security gaps attackers exploit)
- Vendor weaknesses (compromised software before it’s installed)
- Insider risk (social engineering or disgruntled access)
Prevention-first controls for connected environments
- Segment networks so IoT/operational tech can’t freely talk to everything else.
- Apply least-privilege access—people and systems only get what they truly need.
- Encrypt sensitive data at rest and in transit; back it up to multiple secure locations.
- Build cyber requirements into vendor selection and contracts, including incident responsibilities.
What should an incident response plan cover for these threats?
A plan isn’t a binder—it’s a set of practiced decisions. Your playbook should answer:
- Who shuts down access when a suspicious download happens?
- Who escalates and triages “weird prompt” reports from employees?
- How do you isolate affected devices to stop lateral movement?
- How do you communicate internally to reduce repeated exposure during an active event?
Talk through scenarios. If your team has never rehearsed “someone ran a command from a pop-up,” you will waste precious time when it happens.
Key Takeaway

Cyber risk in 2026 is less about “bad clicks” and more about normal behavior in modern workflows. Reduce exposure by training for pull attacks, standardizing safe paths (bookmarks and portals), tightening technical controls, and segmenting connected systems so one mistake doesn’t become a full outage.
FAQ
What is SEO poisoning in simple terms?
SEO poisoning is when attackers manipulate search results so malicious sites appear at the top, increasing the chance employees click and get infected or phished.
How is ClickFix different from phishing?
ClickFix often tricks a user into manually running malicious commands to “fix” a fake issue, instead of relying on a malicious attachment or link alone.
Why are connected warehouses a bigger cyber target?
Connected systems expand attack surfaces, and disruptions can cascade into missed shipments, SLA breaches, and supply chain fallout—making them high-value targets.
What’s one policy that reduces risk quickly?
Require employees to use approved bookmarks/portals for logins and downloads, instead of searching. It cuts off a major route for search-based attacks.
Do we need cyber insurance for these threats?
Insurance can help with incident response and financial fallout, but coverage varies and often depends on security controls and policy wording. The prevention-first move is to reduce likelihood and blast radius first.
A realistic plan for taking action
It can be easy to fall down the rabbit hold when it comes to technology and cyber security. A logical first step is to conduct an internal, high-level assessment. Gain access to our Cyber Resiliency Assessment here.


