Blog
Why Professional Services Firms Need More Than a Basic Business Insurance Package
Professional services firms are not simple office risks. They are trust-based businesses with meaningful liability, cyber, employment, crime, and reputational exposures.

Wage and Hour Mistakes Are a CFO Risk, Not Just an HR Problem
The issue is not simply whether employees are being paid. The issue is whether the business can prove they are being paid correctly.
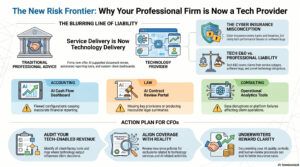
Tech E&O, Cyber Insurance, and AI: Why Professional Services Firms May Now Have Technology Company Risk
Professional services firms using AI, automation, client portals, analytics tools, or software-enabled deliverables may now have Technology Company Risk. Learn why CFOs should review cyber insurance, professional liability, Tech E&O coverage, contracts, and AI controls before a claim occurs.

Six Insurance Coverage Gaps CFOs Should Review Before a Claim Happens
Coverage reviews should go beyond annual pricing comparisons. Learn six common insurance coverage gaps CFOs should evaluate before a claim happens, including equipment breakdown, contingent business interruption, employment practices liability, silent cyber, hired and non-owned auto, and social engineering.

The Hidden Cost of Lifting Injuries: Why Ergonomics Belongs in Your Workers’ Compensation Strategy
Lifting injuries can affect more than employee safety. They can also impact productivity, staffing, workers’ compensation claims, and profitability. Learn how CFOs can use ergonomics, documentation, and prevention-first strategies to reduce risk and control costs.

Cybersecurity Training Is Not Enough: How CFOs Can Build a Culture That Reduces Cyber Risk
Annual cybersecurity training may check a compliance box, but it often falls short of changing employee behavior. Learn how CFOs can support role-specific training, practical controls, and a prevention-first cyber strategy that reduces risk and supports stronger insurance outcomes.
